What if the audience is spies and hackers?
A research security conversation with Dr Brendan Walker-Munro
“There’s a sense that national security threats to the research enterprise and universities is a bit like cancer. It’s, ‘that will happen to somebody else it will never happen to me’. Until it does.”
It’s a question I’d never thought to ask myself, how would I create content to engage spies and hackers? I appreciate that it might sound like a stupid question. Of all the audiences, why spend time, effort, and ultimately money to communicate to potential nation state actors and cyber criminals?
$4,610,000. Give or take $10,000 to $20,000. That’s why.
The average cost of a data breach in the education sector in 2023 was $4,610,0001. Give or take $10,000 to $20,000 is how much some great cyber security content might cost a university2. So, as a potential weapon in the fight against espionage and cyber warfare, I think this would be a wise investment.
The idea was sparked by Dr Brendan Walker-Munro3. A law academic who specialises in research security.
“let’s say, for example, I’m working for an intelligence agency overseas and I’m wanting to come to Australia to try and infiltrate a university… I’m doing my research and I find all of these articles from Australia about how tough their research environment is and how resilient their researchers are and I say ‘maybe we need to reconsider this? Maybe we need to go to a different country? Maybe we need to look at a different way of dong this.’ So, even just having that, kind of, really public facing resolve or resilience in our research enterprise is really important because it can potentially discourage exactly the types of threats that we’re trying to combat.”
He continues
“If you’re a hacker, if you’re someone who’s maybe looking for an easy target you’re not going to go after the organisation, whether it’s a university or otherwise, you’re not going to go after the organisation that is really public about how tough their cybersecurity is. And really engages with industry, talks about the type of work that they’re doing to secure their cybersecurity. You’re going to look at that and go, ‘actually, I might try and pick on someone else because I’m in danger of biting off more than I can chew here’”.
Before we think about what this type of content might look like, it’s worth painting a fuller picture.
Walker-Munro presents a chilling scenario.
“You might be cooperating with a foreign entity and you might think ‘yep, they’re 100% above board. They’re, you know, always honest with me, I’d trust them with my kids’ basically. But at the same time, they might work in a country where the security services comes and knocks on your door and says ‘we want to know everything about what you’re doing’. They can’t say no, or you know, they might be harmed, they might end up in jail, they might, basically, just disappear.”
Identifying further challenges, Walker-Munro reflects on a conversation with a professor. He was told, “we know the threat from China, but that’s where the money is”.
Even though awareness and engagement are critical for securing the nation’s universities, their data and intellectual property, for many institutions education isn’t a top priority. But with a dramatic rise in industry and government partnered research projects, particularly at the bleeding edge of artificial intelligence and aerospace, both the value of research data and IP and the intensity of threats will skyrocket.
The graphic below illustrates Australian universities’ priorities when it comes to countering foreign interference.
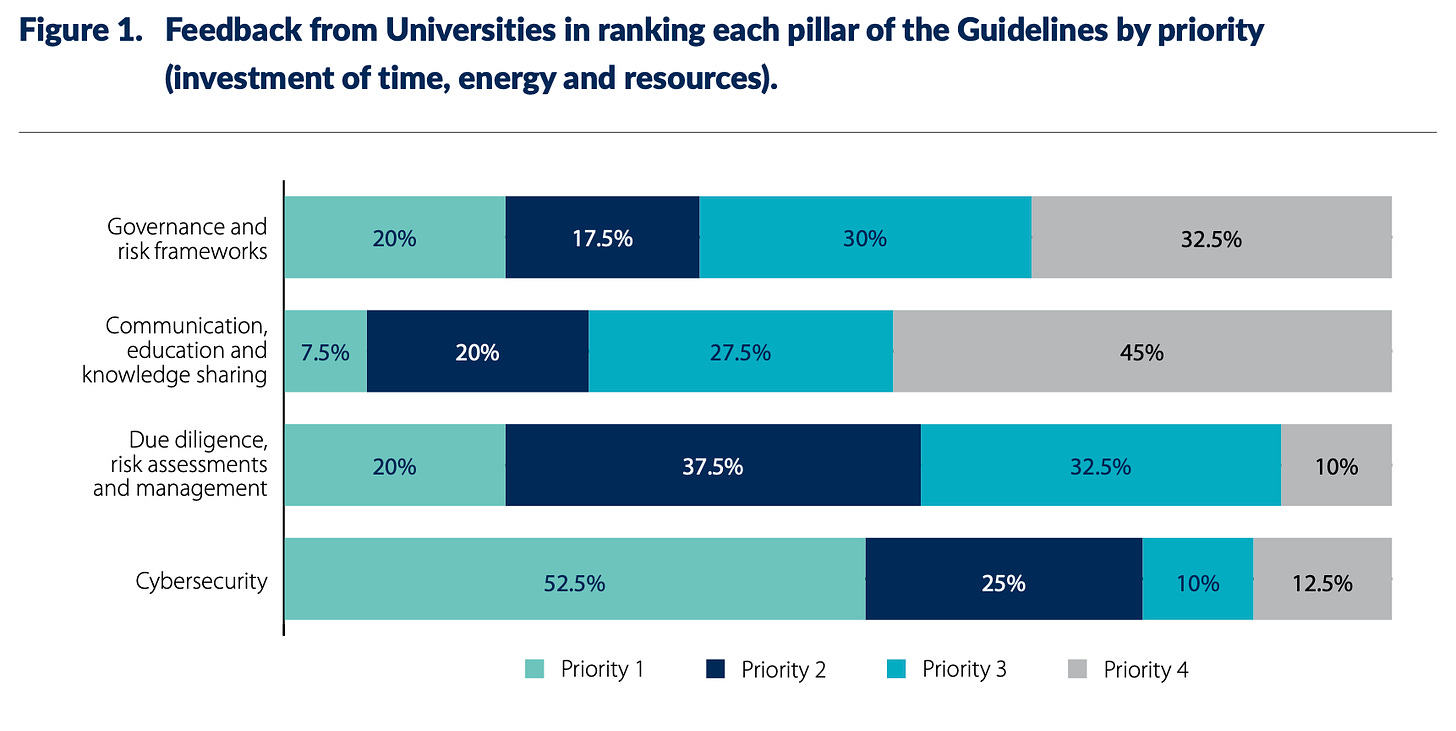
It’s understandable that cybersecurity is Priority 1 for over 50% of institutions. This also illustrates the scale, and fear, of the cyber threat. But as places of teaching and research it is alarming that 45% of universities rank education and knowledge sharing as Priority 4, or last. Mind you, it is encouraging that two or three universities in Australia believe that education is the best defence.
There are countless articles that discuss why and how humans can be the weakest link in an organistion’s cybersecurity. No matter how robust your technical defences are they can still be rendered useless by a sophisticated social engineering campaign. On a positive flip side, in stark juxtaposition to the idea that human’s are the weakest link, through education you can empower the university community with the tools to identify and avert these attacks in ways which technology alone can’t. From what might be a simple phishing or payroll scam to espionage in your research laboratories.
Walker-Munro, too, believes that education, engagement and awareness is critical.
“So, just under half think that education and awareness piece is actually the least important and, kind of, it’s we need to worry about some other stuff first. I would say it is probably the opposite direction. And, precisely because there’s not just a misunderstanding about the nature of the threat. It’s also about a misunderstanding of what this whole system of research security is intended to achieve.”
On the topic of foreign interference and the risk of cyber threats, what does the report say about education and awareness?
“universities have gained more awareness of the risks that face the sector and have implemented training to ensure their staff are adequately informed and prepared to manage these risks.”
“While many executive and senior staff at universities are engaged in countering foreign interference, some parts of the sector commented on the need for education and knowledge sharing to occur at all levels of staff, and amongst students.”
The report goes on to state
“Many universities have found it challenging to communicate the risks of foreign interference to staff and students… Many universities commented that the need to develop in-house training and guidance materials was burdensome on time and financial resourcing.”
This challenge is echoed by Walker-Munro.
Considering whether academics are prepared and understand the risks, he notes a certain response
“I’m not going to have someone spy on me, I’m not very important”.
He contrasts this response with the private sector.
“‘Oh yeah, we’ve known about this in the business world for decades’… Big organisations have been grappling with these problems… so I think that the, kind of, having the blinkers on is a problem you can really only confront by consistently getting out there and consistently talking about the topic.”
So, institutions are aware of the need for education and awareness. And while some efforts have been made, it will be a constant battle to stay ahead of the threats and to keep the university community engaged, aware, and vigilant.
This will be a tough job, but a critical one.
May I remind you of that rather large number. $4,610,0004.
When it comes to cybersecurity engagement you can, though quite crudely, divide the audience into technical and non-technical. For non-technical audiences, consider The cyber philosopher through a corporate lens.
But let’s remember our aim: expressing the university’s cybersecurity capabilities to prospective spies and cyber criminals.
So the objectives are:
Demonstrate the university’s cybersecurity capabilities and capacity to defend sophisticated cyber attacks
Position the university as a leader in cyber security research, and actually applying this research in the field with industry partners
Raise the university’s profile in the cybersecurity community
All of the above can be achieved with creative content, and I envision a podcast with accompanying YouTube channel.
Centering on academics and their industry partners, research translation will play a critical role. Superficial repackaging of industry news and other creators’ ideas won’t cut through, or resonate with audiences in any meaningful way. Just another podcast with little to offer. Instead, by focusing on the institution’s own cybersecurity research and its application, the university will position itself as a heavy hitter worthy of attention and respect.
But do spies and hackers actually listen to podcasts or watch videos? I don’t know5. But if we think about Walker-Munro’s scenario of an intelligence agent infiltrating an Australian university
“I’m doing my research and I find all of these…”
The content needs to be accessible, and compared to academic publications, podcasts and videos are far more discoverable.
So this is the proposal in a nutshell.
Create great content > be respected by the community > grow an audience of cyber professionals > be known as an institution that is at the forefront of cybersecurity research and practice > don’t get hacked!
Maybe it is that easy?6
For more cybersecurity reading, check out Cybersecurity is boring and The cyber philosopher.
Check this out if you’re interested in making better research videos.
IBM Security’s Cost Of Data Breach Report 2023, and more information on data breaches in Australia. It is worth noting that this figure is the average cost of a data breach. For research institutions, the cost of an act of cyber espionage could be far more expensive. Industry and government partnerships are worth millions of dollars. Not to mention the intangible value of reputation and prestige that comes with such partnerships. This could all be lost.
This is a rough ballpark figure. A podcast series might cost as little as a few thousand dollars, a full creative campaign could easily cost more than $20,000. The point is, in comparison to the cost of a data breach the cost of some great creative cybersecurity content is insignificant in the context of its potential ROI (i.e.: not getting hacked in the first place).
A Senior Lecturer in Law at Southern Cross University, he also writes great pieces for public engagement for publishers including The Conversation.
A quick note to acknowledge that this article does conflate the threats of cyber attack and foreign interference. There is a lot of data available on the cost of data breaches, while the research security landscape is far less known. The Australian National University appears in a list of top 10 Australian data breaches, and a quick search uncovers data breaches at University of Sydney, University of Wollongong, Deakin University, University of Western Australia, and Queensland University of Technology. The threat of cyber attacks is constant. Up until now, these breaches have been primarily personal information. Is it only a matter of time before cyber actors are successful in stealing research secrets? In Walker-Munro’s words, “So perhaps we should act now, before we get a scandal to spur us into action.”
Surely, even black hat hackers listen to popular cybersecurity podcasts like Darknet Diaries and Malicious Life? While thinking about the audience, something that strikes me about this campaign idea, something that is quite unusual, is that the primary audience does not align with the aim. That is to say, even though the aim is to express the university’s cyber capabilities to spies and cyber criminals black hat hackers aren’t the primary audience. White and grey hat hackers are, as well as blue teams and incident responders. But by building a solid following of cybersecurity professionals more broadly, the university’s content is more likely to be discovered.
It isn’t really that easy. This is just one small piece of a university’s cybersecurity education, awareness and engagement mission. But it is perhaps the piece that hasn’t been addressed by the cybersecurity awareness market because of the unique environment in which research is conducted (and with its own unique set of challenges). An off the shelf “cyber awareness” app/content subscription/short course/cert just isn’t going to have the nuance required. If we think back to the report, “Many universities commented that the need to develop in-house training and guidance materials was burdensome on time and financial resourcing”. Well, get infiltrated them.